Latest News
Alexandra Peter's collection of historic samplers includes items from the family of "The House of the Seven Gables" author Nathaniel Hawthorne.
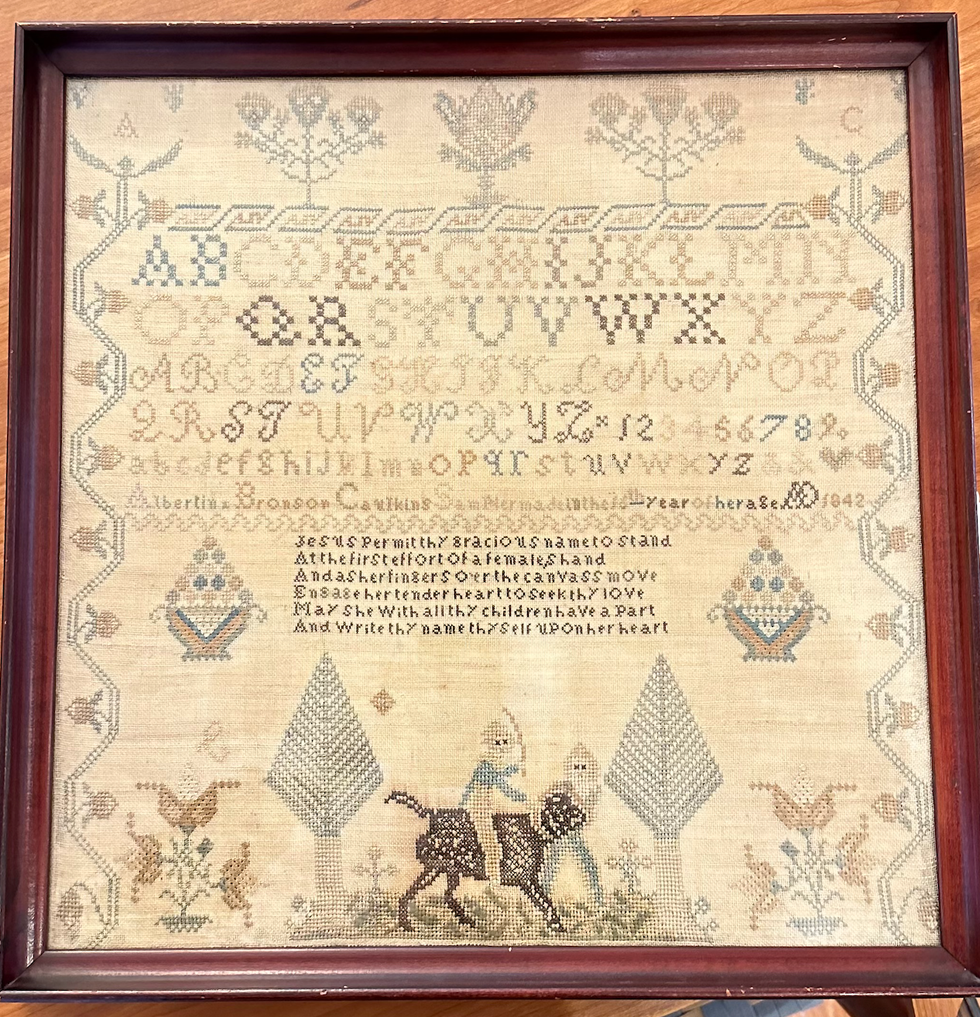
The home in Sharon that Alexandra Peters and her husband, Fred, have owned for the past 20 years feels like a mini museum. As you walk through the downstairs rooms, you’ll see dozens of examples from her needlework sampler collection. Some are simple and crude, others are sophisticated and complex. Some are framed, some lie loose on the dining table.
Many of them have museum cards, explaining where those samplers came from and why they are important.
It’s not that Peters has delusions of grandeur, with those small black or white cards a part of the fantasy. In the past few years, her samplers have gone on outings to historical societies and exhibits. Those small black cards are souvenirs.
About 27 of the pieces from Peters’ collection have just left home again, and are featured at the Litchfield History Museum of the Litchfield Historical Society in an exhibit that Peters guest curated along with the historical society’s curator of collections, Alex Dubois.
The exhibit is called “With Their Busy Needles,” and it opens with a reception on Friday, April 26, from 6 to 8 p.m. (The exhibit will remain open until the end of November.) Peters will give a talk called “Know My Name: How Schoolgirls’ Samplers Created a Remarkable History” at the museum on Sunday, May 5, at 3 p.m.
Although Peters was first attracted to samplers as a form of art and craft, she has come to see them as something more profound. Each sampler tells a story, but you have to know how to read between the lines of thread and fabric. Peters has become an able and eloquent curator of what were once educational tools just for young girls and women. She can look at one and give an educated guess about who made it, how old they were, where they lived and how affluent their family was (or wasn’t).
Some samplers were made on linen, others were made with silk. Some linens are fine, others are rough and homespun.
“Some of my favorites are made on what’s called ‘linsey woolsey,’” Peters said. “It’s a mix of linen and wool that’s been dyed green. It was uncomfortable to wear, but it looks great on a sampler!”
Younger girls often worked first on learning darning stitches, and would make simple samplers with letters of the alphabet. More advanced stitchers might create genealogies or family trees. Peters particularly loves to find multiple examples from one family.
“I have a couple sets that were done by sisters,” she said, “and a collection from the family of Nathaniel Hawthorne,” the American author of “The Scarlet Letter.”
All samplers, though, show the importance of girls within families, Peters said.

“Parents were excited about their girls getting an education and coming out in the world and displaying their accomplishments. It’s different from what we think.”
“We tend to scorn or disrespect things made by women, particularly if they’re domestic. But before the Industrial Revolution, all work was done at the home, by women and by men. There weren’t jobs that you went to, you did the work at home. Samplers, and needlework, are the work of women, the work of girls.”
Samplers were rarely sold, Peters said, except ones made to help Southern Blacks to escape slavery.
“They were made anonymously and sold at anti-slavery fairs from the 1830s to the 1860s. I have one that can be used as a potholder and it says, ‘Any holder but a slaveholder.’ I have another that must have been a table runner that says, ‘We’s free!’ We’d see some of them as offensive now, but they weren’t at the time; they were joyful.”
Every sampler tells a story, and Peters is an able and entertaining interpreter of those tales. Learn more by visiting the Litchfield History Museum and seeing the exhibit (complete with explanatory museum cards) and come for her talk about samplers on May 5. Register for the opening reception and for the talk at www.litchfieldhistoricalsociety.org/exhibitions.
Oscar Lock, a Hotchkiss senior, got pointers and encouragement from Tim Hunter, stewardship director of The Sharon Land Trust, while sawing buckthorn.
It was a ramble through bramble on Wednesday, April 17 as a handful of Hotchkiss students armed with loppers attacked a thicket of buckthorn and bittersweet at the Sharon Land Trust’s Hamlin Preserve.
The students learned about the destructive impact of invasives as they trudged — often bent over — across wet ground on the semblance of a trail, led by Tom Zetterstrom, a North Canaan tree preservationist and member of the Sharon Land Trust.
The return of students on this working walkthrough was part of Hotchkiss’s Fairfield Farm Ecosystem and Adventure Team, a program that incorporates environmental stewardship in the learning experience.
The Hamlin Preserve is a 210-acre property with 2.5 miles of trails, and the Hamlin conifer grove restoration is a large-scale landscape forest preservation project.

The group entered at the end of Stone House Road and proceeded into an invasive thicket that has already taken its toll on cedars and pines. Zetterstrom stopped the group for several lecture moments and demonstrations of the proper way to cut bittersweet.
Tim Hunter, stewardship director of the Trust, pulled out a folding handsaw that student Oscar Lock, a senior, used to sever a buckthorn at ground level.
Shaye Lee, a sophomore, took a turn with the saw on some privet.
As the group huddled under a close canopy of invasive vegetation that was overtaking everything in sight, Zetterstrom explained that invasive-laden patch was once productive farmland.
As the two-hour stroll-and-lop ended, the group assembled in a hay field on the property to observe a healthy American elm at the edge of the open field that has been saved by the Trust’s efforts.
Pointing to Red Mountain in the short distance, Zetterstrom told the students: “When you come back for your reunions — maybe in 50 years — you can say I helped save those trees.”












